Sign up for our public-beta program and redeem upwards of $1.000 USD in Zalter credits for your first year!
Real Security— Revolutionary and Innovative Protocol.
Zalter Identity offers a brand new series of authentication protocols and identity checking technology meant to protect even against active MITM.
Prevent Account Takeover Fraud
Email Magic Link
Simple and secure sign in links sent via email
Email One-Time-Passcode
Sign in users with a one-time passcode sent via email
SMS One-Time-Passcode
Sign in users with a one-time passcode sent via SMS
Multi-Factor Authentication
Add extra factors such as Google Authenticator
Advanced Security: Checked
Easily deploy Man-in-the-Middle attack resistant auth system & Multi-Factor Authentication (MFA). Stop all attacks, including ransomware, push attacks and account takeover with passwordless authentication secured by public-key cryptography and full-request signatures.
End-to-end encryption. During the authentication, a new end to end encryption system protocol ensures no active or passive MITM attack is effective
No cookies used. We not use cookies to function, so even if the user browser doesn't accept cookies, the authentication will still work
Private credentials. The private key never leaves the browser and can never be stolen by MITM attacks. After the authentication, signatures guarantee the user claims
1async function signRequest(requestInit) {
2 const { method, headers, body } = requestInit;
3
4 // Load current user and get their public key ID
5 const user = await auth.getCurrentUser();
6 const keyId = user.subSigKeyId;
7
8 const data = Buffer.from(body || Buffer.alloc(0));
9
10 // Create the signature by signing the message
11 let sig = await user.signMessage(data);
12
13 // Encode the signature to Base64
14 sig = Buffer.from(sig).toString('base64');
15
16 return {
17 method,
18 headers: {
19 ...headers,
20 // Add the signature header
21 'x-signature': `${keyId};${sig}`
22 },
23 body
24 };
25}Easy Integration
Identity client libraries provide a simple API interface to build custom sign in experiences for your app in a few lines of code.
Read the docsAvailable SDKs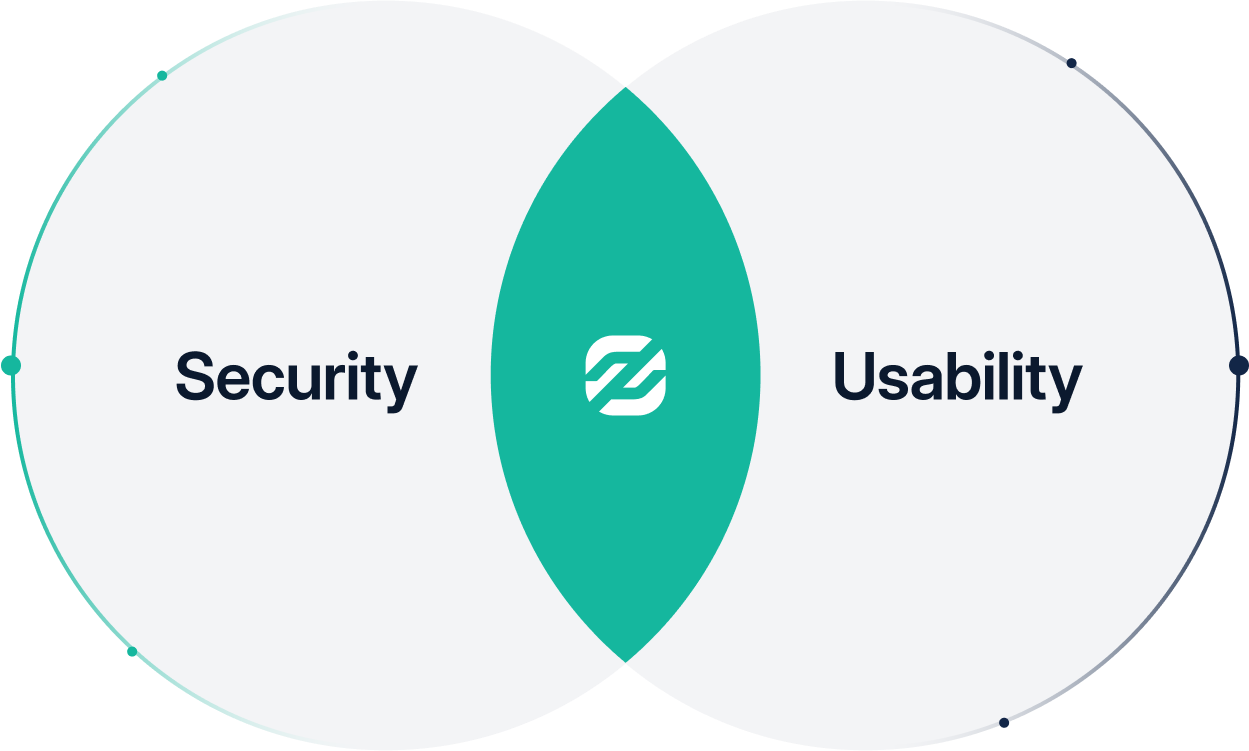
Balancing Security and Usability
Zalter Identity focuses on security, and both developer and user experience. Usually, one has to make compromises on security to achieve a good experience, but here's not the case. Deliver an optimized and easy authentication process to ensure your organization can acquire customers quickly and securely.
Start authenticating for free
Get in touch or start integrating
Jump into the developers docs and start building in minutes
Zalter is free to get started and scales with you as you grow.
Get a free personalized demo from a security expert.